 Drift protocol (DRIFT)
Drift protocol (DRIFT)
$0.04236 +2.22% 24H
- 16社交熱度指數(SSI)-64.01% (24h)
- #76市場預警排名(MPR)-34
- 824小時社交提及量-68.00% (24h)
- 0%24小時KOL看好比例8位活躍KOL
- 概要
- 看漲訊號
- 看跌訊號
社交熱度指數(SSI)
- 總體資料16SSI
- 社交熱度趨勢(7D)價格(7D)情緒分佈中性 (13%)看跌 (38%)極度看跌 (49%)社交熱度洞察
市場預警排名(MPR)
- 預警解讀
相關推文
- 釋出後DRIFT走勢極度看跌
 Sherry 🇻🇳 Community_Lead DeFi_Expert B4.61K @sherryonchain
Sherry 🇻🇳 Community_Lead DeFi_Expert B4.61K @sherryonchain LE HOANG TRONG 🟦 D10.03K @Trong0322
LE HOANG TRONG 🟦 D10.03K @Trong0322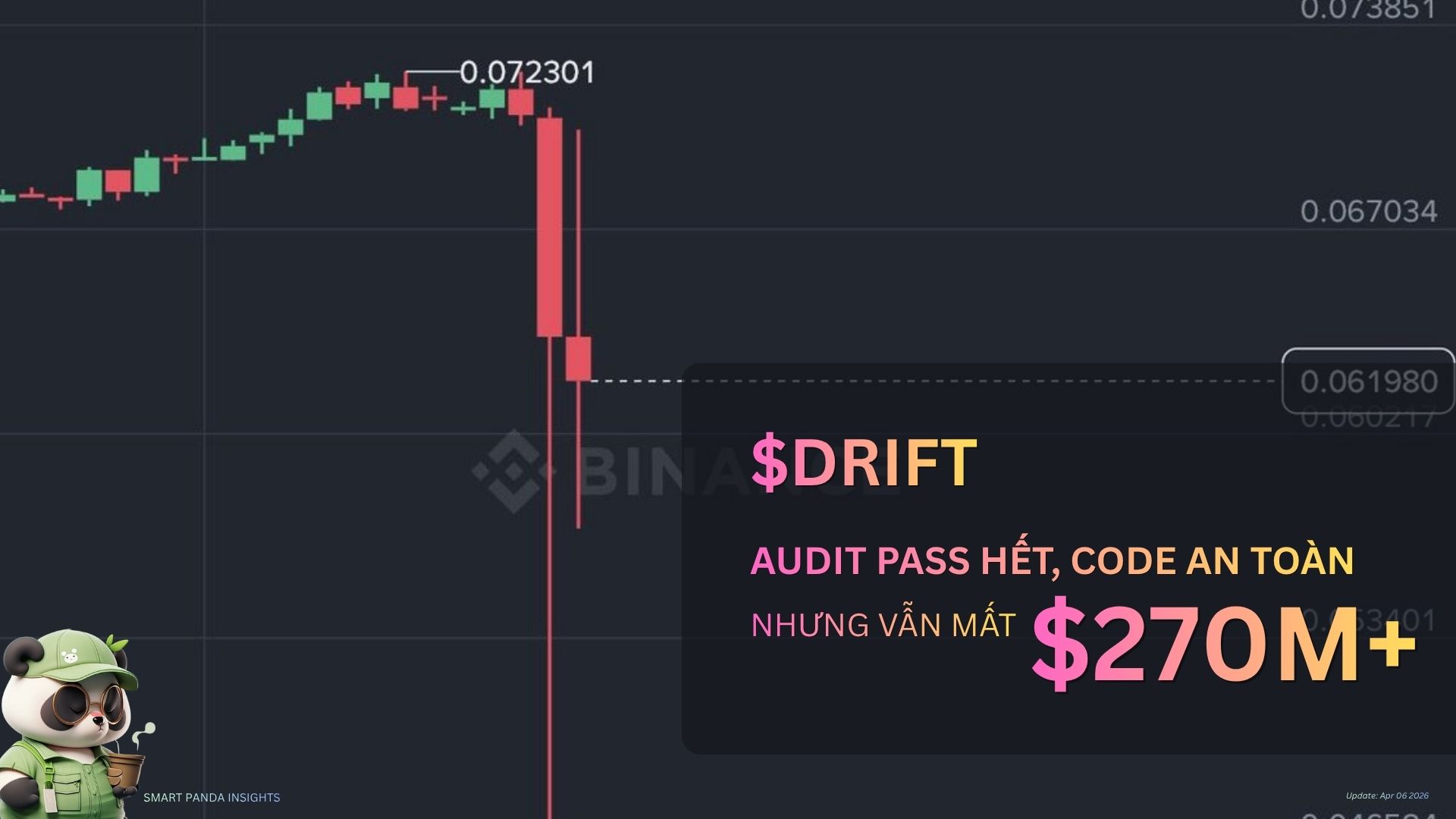 35 7 3.64K 閱讀原文 >釋出後DRIFT走勢極度看跌
35 7 3.64K 閱讀原文 >釋出後DRIFT走勢極度看跌- 釋出後DRIFT走勢極度看跌
 NoFuture Trader Influencer C12.67K @nofuture
NoFuture Trader Influencer C12.67K @nofuture
 NoFuture Trader Influencer C12.67K @nofuture
NoFuture Trader Influencer C12.67K @nofuture NoFuture Trader Influencer C12.67K @nofuture
NoFuture Trader Influencer C12.67K @nofuture NoFuture Trader Influencer C12.67K @nofuture
NoFuture Trader Influencer C12.67K @nofuture NoFuture Trader Influencer C12.67K @nofuture
NoFuture Trader Influencer C12.67K @nofuture NoFuture Trader Influencer C12.67K @nofuture10 7 98 閱讀原文 >釋出後DRIFT走勢中性
NoFuture Trader Influencer C12.67K @nofuture10 7 98 閱讀原文 >釋出後DRIFT走勢中性- 釋出後DRIFT走勢看跌
- 釋出後DRIFT走勢看跌
- 釋出後DRIFT走勢看跌
 𝙶𝙶 TA_Analyst Influencer B12.42K @ggcripto
𝙶𝙶 TA_Analyst Influencer B12.42K @ggcripto Criptovaluta.it D30.40K @CriptovalutaI
Criptovaluta.it D30.40K @CriptovalutaI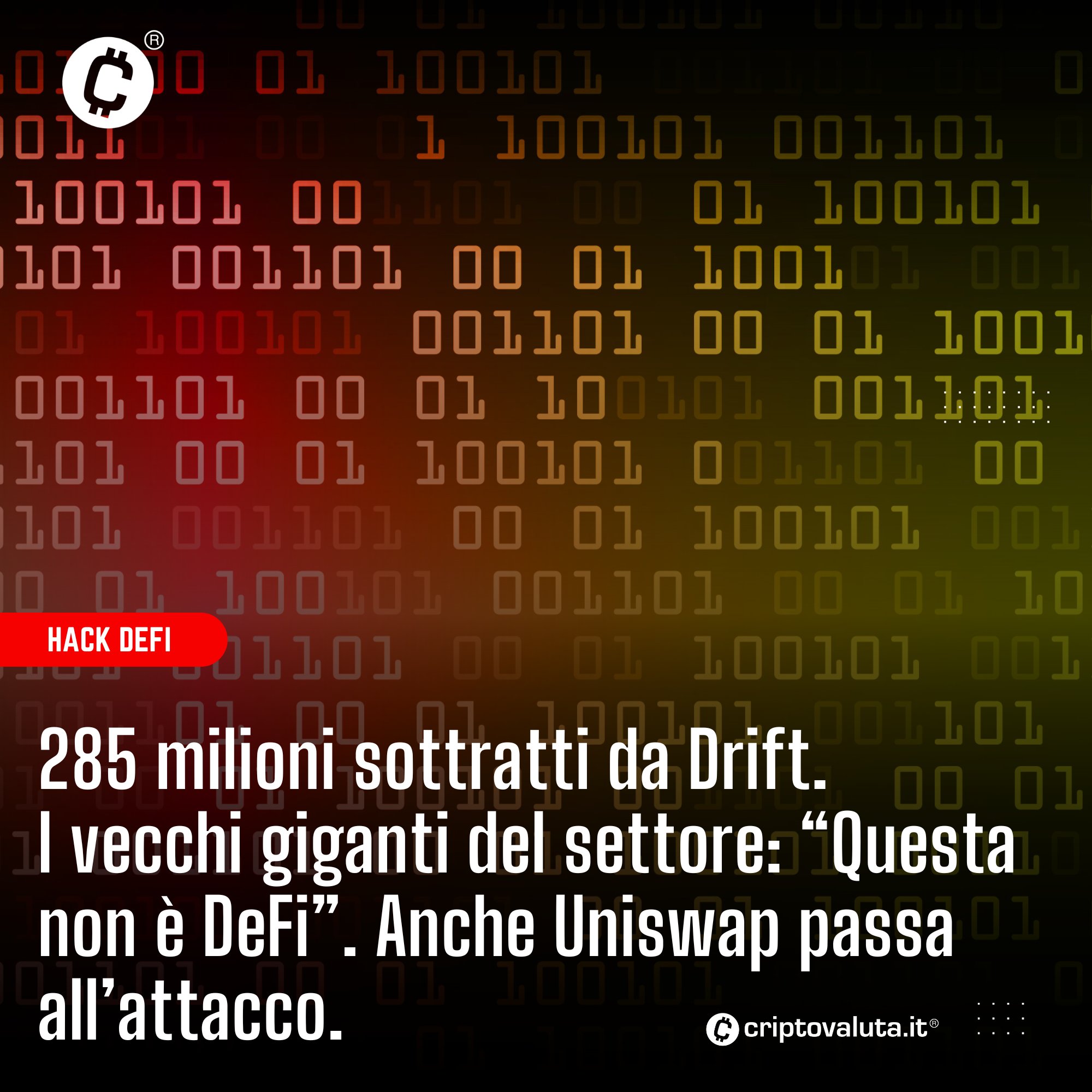 10 1 1.01K 閱讀原文 >釋出後DRIFT走勢極度看跌
10 1 1.01K 閱讀原文 >釋出後DRIFT走勢極度看跌- 釋出後DRIFT走勢看跌
 Caitlin Long 🔑⚡️🟠 Founder Regulatory_Expert B250.50K @CaitlinLong_
Caitlin Long 🔑⚡️🟠 Founder Regulatory_Expert B250.50K @CaitlinLong_ Watcher.News D64.07K @watchernewsx12 3 8.22K 閱讀原文 >釋出後DRIFT走勢看跌
Watcher.News D64.07K @watchernewsx12 3 8.22K 閱讀原文 >釋出後DRIFT走勢看跌