 THORChain (RUNE)
THORChain (RUNE)
$0.4598 -21.33% 24H
- 74Soziale-Stimmungs-Index (SSI)+213.28% (24h)
- #2Marktimpuls-Ranking (MPR)+70
- 8624-St. in Social Media+8,600.00% (24h)
- 3%24 Std-Bullisch-Verhältnis73 aktive Meinungsbildner
- Zusammenfassung
- Bullische Signale
- Bärische Signale
Soziale-Stimmungs-Index (SSI)
- Daten insgesamt74SSI
- SSI-Trend (7-Tage)Preis (7 Tage)StimmungsverteilungBullisch (3%)Neutral (2%)Bärisch (34%)Extrem bärisch (61%)SSI Einblicke
Marktimpuls-Ranking (MPR)
- Warnungseinblick
Beiträge auf X
 crypto.news Media Influencer C117.70K @cryptodotnews
crypto.news Media Influencer C117.70K @cryptodotnews
 crypto.news Media Influencer C117.70K @cryptodotnews
crypto.news Media Influencer C117.70K @cryptodotnews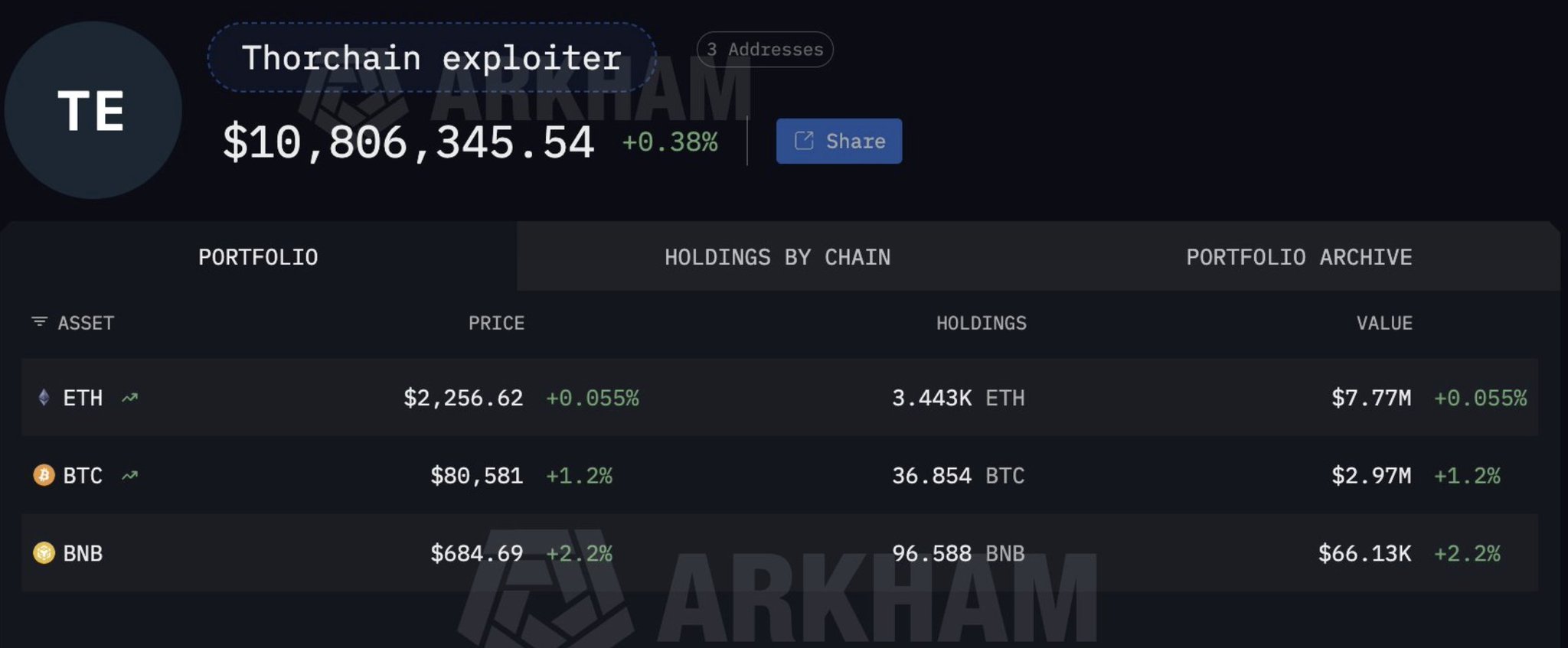 2 0 280 Original lesen >Trend von RUNE nach VeröffentlichungExtrem bärisch
2 0 280 Original lesen >Trend von RUNE nach VeröffentlichungExtrem bärisch KenErik Community_Lead Influencer C2.24K @kenerik
KenErik Community_Lead Influencer C2.24K @kenerik KenErik Community_Lead Influencer C2.24K @kenerik1 0 60 Original lesen >Trend von RUNE nach VeröffentlichungBärisch
KenErik Community_Lead Influencer C2.24K @kenerik1 0 60 Original lesen >Trend von RUNE nach VeröffentlichungBärisch Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr
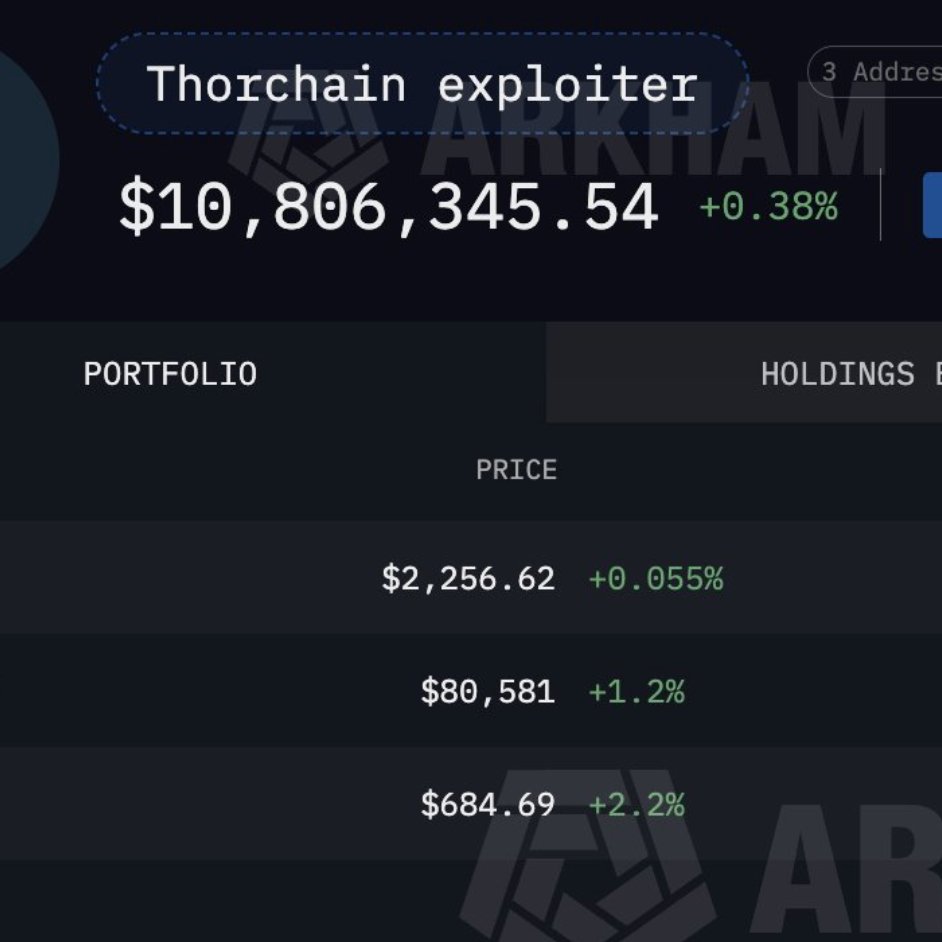
Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr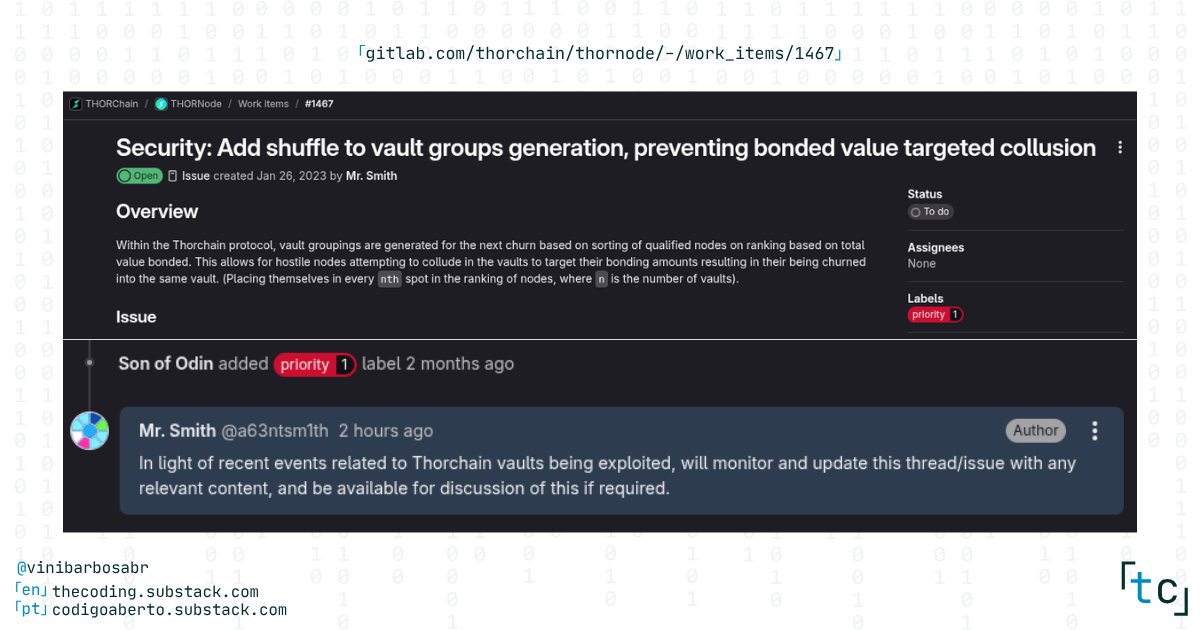 25 2 2.85K Original lesen >Trend von RUNE nach VeröffentlichungExtrem bärisch
25 2 2.85K Original lesen >Trend von RUNE nach VeröffentlichungExtrem bärisch z80.wei 👌☀️👌 Dev Security_Expert B8.27K @0xz80
z80.wei 👌☀️👌 Dev Security_Expert B8.27K @0xz80 Charles Guillemet Security_Expert Researcher B43.16K @P3b7_7 0 320 Original lesen >Trend von RUNE nach VeröffentlichungBärisch
Charles Guillemet Security_Expert Researcher B43.16K @P3b7_7 0 320 Original lesen >Trend von RUNE nach VeröffentlichungBärisch KenErik Community_Lead Influencer C2.24K @kenerik
KenErik Community_Lead Influencer C2.24K @kenerik Charles Guillemet Security_Expert Researcher B43.16K @P3b7_1 0 76 Original lesen >Trend von RUNE nach VeröffentlichungExtrem bärisch
Charles Guillemet Security_Expert Researcher B43.16K @P3b7_1 0 76 Original lesen >Trend von RUNE nach VeröffentlichungExtrem bärisch spuddy Dev OnChain_Analyst B1.68K @0xSpuddy
spuddy Dev OnChain_Analyst B1.68K @0xSpuddy Charles Guillemet Security_Expert Researcher B43.16K @P3b7_289 30 49.93K Original lesen >Trend von RUNE nach VeröffentlichungExtrem bärisch
Charles Guillemet Security_Expert Researcher B43.16K @P3b7_289 30 49.93K Original lesen >Trend von RUNE nach VeröffentlichungExtrem bärisch Preetam 📍 NYC 🇺🇲 Security_Expert Founder B5.92K @raopreetam_
Preetam 📍 NYC 🇺🇲 Security_Expert Founder B5.92K @raopreetam_ Charles Guillemet Security_Expert Researcher B43.16K @P3b7_289 30 49.93K Original lesen >Trend von RUNE nach VeröffentlichungBärisch
Charles Guillemet Security_Expert Researcher B43.16K @P3b7_289 30 49.93K Original lesen >Trend von RUNE nach VeröffentlichungBärisch tochi Trader Educator B70.84K @oxtochi
tochi Trader Educator B70.84K @oxtochi tochi Trader Educator B70.84K @oxtochi77 26 1.63K Original lesen >Trend von RUNE nach VeröffentlichungBärisch
tochi Trader Educator B70.84K @oxtochi77 26 1.63K Original lesen >Trend von RUNE nach VeröffentlichungBärisch- Trend von RUNE nach VeröffentlichungBullisch
- Trend von RUNE nach VeröffentlichungExtrem bärisch