 THORChain (RUNE)
THORChain (RUNE)
$0.4396 -15.36% 24H
- 74Social Sentiment Index (SSI)- (24h)
- #1Market Pulse Ranking (MPR)0
- 9724h Social Mention- (24h)
- 3%24h KOL Bullish Ratio77 Active KOL
- Summary
- Bullish Signals
- Bearish Signals
Social Sentiment Index (SSI)
- Data Overall74SSI
- SSI Trend (7D)Price (7D)Sentiment DistributionBullish (3%)Neutral (2%)Bearish (36%)Extremely Bearish (59%)SSI Insights
Market Pulse Ranking (MPR)
- Alert Insight
X Posts
- Trend of RUNE after releaseExtremely Bearish
 蓝狐 OnChain_Analyst Security_Expert B73.19K @lanhubiji
蓝狐 OnChain_Analyst Security_Expert B73.19K @lanhubiji 蓝狐 OnChain_Analyst Security_Expert B73.19K @lanhubiji
蓝狐 OnChain_Analyst Security_Expert B73.19K @lanhubiji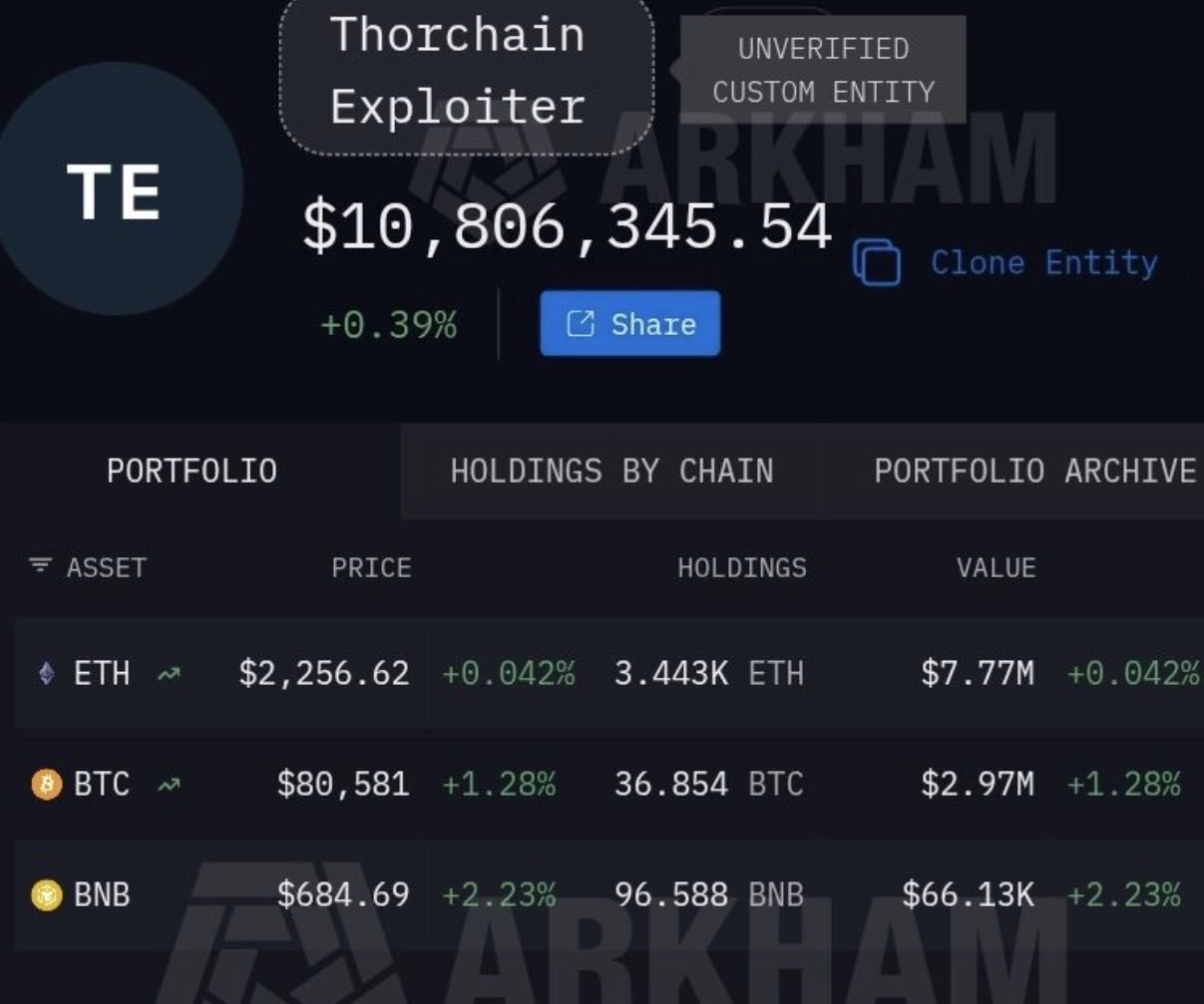 10 5 2.64K Original >Trend of RUNE after releaseBearish
10 5 2.64K Original >Trend of RUNE after releaseBearish Cryptosailor Dev Researcher B2.21K @robertdavid010
Cryptosailor Dev Researcher B2.21K @robertdavid010 Chainalysis D63.16K @chainalysis158 10 19.87K Original >Trend of RUNE after releaseBearish
Chainalysis D63.16K @chainalysis158 10 19.87K Original >Trend of RUNE after releaseBearish- Trend of RUNE after releaseExtremely Bearish
 Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret
Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret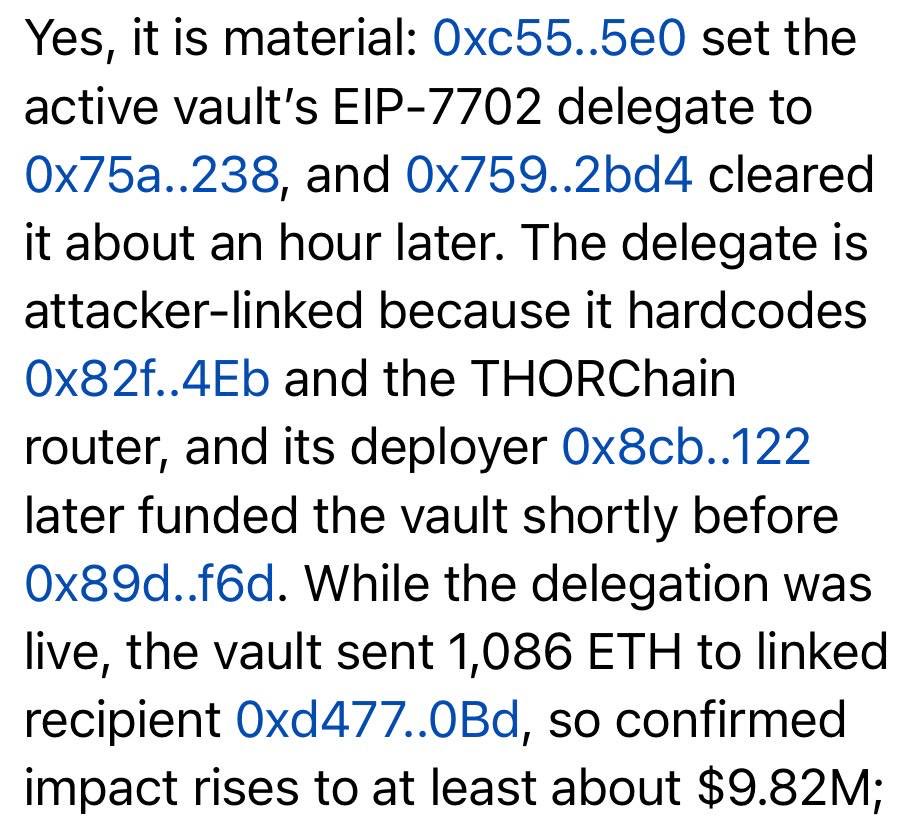
 Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret
Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret
Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret
Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret26 2 2.91K Original >Trend of RUNE after releaseExtremely Bearish
Vladimir S. | Officer's Notes Security_Expert Researcher S51.22K @officer_secret26 2 2.91K Original >Trend of RUNE after releaseExtremely Bearish Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr
Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr54 5 5.20K Original >Trend of RUNE after releaseBearish
Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr54 5 5.20K Original >Trend of RUNE after releaseBearish Vadim (AI, ⋈) OnChain_Analyst Security_Expert S12.47K @zacodil
Vadim (AI, ⋈) OnChain_Analyst Security_Expert S12.47K @zacodil THORChain D288.77K @THORChain278 19 45.31K Original >Trend of RUNE after releaseBearish
THORChain D288.77K @THORChain278 19 45.31K Original >Trend of RUNE after releaseBearish- Trend of RUNE after releaseExtremely Bearish
 Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr
Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr
Vini B |「 thecoding 」 Security_Expert OnChain_Analyst B11.38K @vinibarbosabr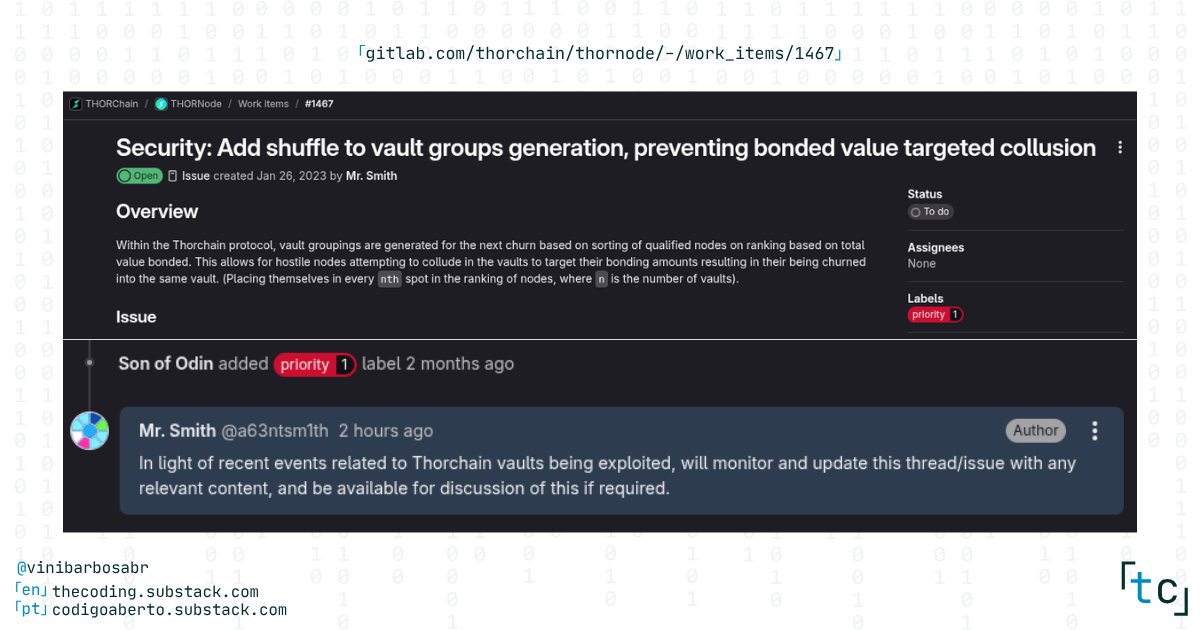 31 2 4.25K Original >Trend of RUNE after releaseBearish
31 2 4.25K Original >Trend of RUNE after releaseBearish crypto.news Media Influencer C117.70K @cryptodotnews
crypto.news Media Influencer C117.70K @cryptodotnews
 crypto.news Media Influencer C117.70K @cryptodotnews
crypto.news Media Influencer C117.70K @cryptodotnews 10 1 1.42K Original >Trend of RUNE after releaseExtremely Bearish
10 1 1.42K Original >Trend of RUNE after releaseExtremely Bearish